AI Hacked! LiteLLM COMPROMISED! 97 Million Potentially Exposed
LiteLLM has been compromised in a major supply chain attack affecting an estimated 97 million monthly downloads. Versions 1.82.7 and 1.82.8 on PyPI contain malicious code that steals SSH keys, cloud credentials, API keys, Kubernetes configs, crypto wallets, and environment variables. The malware runs automatically on install (via a .pth file in 1.82.8) or on import (in 1.82.7), encrypts stolen data with AES-256-CBC and RSA-4096, and exfiltrates it to a fake domain models.litellm.cloud.
This attack was carried out by the threat group TeamPCP, which previously compromised security tools like Trivy and Checkmarx. The breach likely originated from a compromised CI/CD pipeline used by LiteLLM’s maintainers, who were likely targeted via the Trivy supply chain attack.
Critical actions immediately:
- Stop using any version of LiteLLM 1.82.7 or 1.82.8.
- Downgrade to version 1.82.6 or pin your dependency to
litellm<=1.82.6. - Rotate all credentials on any system that had the compromised version installed—this includes cloud keys, API keys, SSH keys, and CI/CD secrets.
- Audit network logs for outbound connections to
models.litellm.cloud. - Review Docker images and CI/CD pipelines built in the last 48 hours.
- The entire LiteLLM package has been pulled from PyPI, and the attack is part of a coordinated campaign targeting high-trust developer infrastructure.
What Does The KJV Bible Say?
On March 24, 2026, the popular AI orchestration library LiteLLM was compromised in a major supply chain attack. Malicious actors from the group TeamPCP gained access to the project’s PyPI publishing credentials through a prior breach of the Trivy security scanner used in LiteLLM’s CI/CD pipeline.
While the “97 million” figure refers to LiteLLM’s monthly download volume, the actual number of compromised machines is estimated to be approximately 500,000, with roughly 300GB of sensitive data exfiltrated.
Incident Overview: LiteLLM Supply Chain Breach
The attack involved publishing backdoored versions of the package that contained a credential harvester and a Kubernetes lateral movement toolkit.
| Feature | Incident Details |
|---|---|
| Date | March 24, 2026 |
| Affected Versions | v1.82.7 and v1.82.8 |
| Attacker Group | TeamPCP |
| Estimated Impact | 500,000 machines / 300GB data stolen |
| Exfiltrated Data | SSH keys, AWS/GCP/Azure credentials, Kubernetes configs, API keys, crypto wallets, and environment variables |
| Root Cause | Stolen PyPI token via compromised Trivy scanner |
| Current Status | Malicious versions quarantined; use v1.82.6 or earlier |
10 Examples of “Banding” (Impact Levels)
“Banding” in this context refers to the varying degrees of exposure based on how LiteLLM was integrated into a developer’s environment.
- Direct Local Install: Running
pip install litellmwithout pinning a version resulted in an immediate download of the poisoned v1.82.8. - CI/CD Pipeline Exposure: Automated build agents that re-installed dependencies daily were compromised, leaking secrets stored in environment variables.
- Transitive Dependency: Projects using AI frameworks (like DSPy) that depend on LiteLLM were unintentionally infected if those frameworks did not pin LiteLLM versions.
- Persistent Python Backdoor: Version 1.82.8 installed a
.pthfile, causing the malicious code to run during any Python execution on the machine, even if LiteLLM wasn’t imported. - Cloud Infrastructure Access: Exposed AWS/GCP/Azure credentials allowed attackers to potentially access live cloud environments.
- Kubernetes Lateral Movement: The malware scanned for K8s service account tokens to read cluster secrets across all namespaces.
- SSH Identity Theft: Stolen SSH private keys allowed attackers to access remote servers and repositories.
- Crypto Wallet Theft: Encrypted wallets found on development machines were specifically targeted for exfiltration.
- Vibe-Coded Impersonation: AI agents running on compromised machines could be manipulated to perform actions or exfiltrate data from private files.
- Containerized Environments: Users of the LiteLLM proxy Docker image remained safe, as those images typically use pinned, verified versions.
20-Question Security Awareness Test
1. What was the primary method used to attack LiteLLM?
- A) SQL Injection
- ✅ B) Supply Chain Attack (via PyPI)
- C) DDoS Attack
- D) Social Engineering
2. Which versions of LiteLLM were confirmed to be malicious?
- A) 1.0.0 and 1.1.0
- B) 1.81.5 and 1.81.6
- ✅ C) 1.82.7 and 1.82.8
- D) All versions after 2.0.0
3. How did the attackers gain access to LiteLLM’s publishing credentials?
- A) Brute-forcing the password
- B) Phishing the maintainer
- ✅ C) Compromising the Trivy security scanner used in the CI/CD pipeline
- D) Exploiting a GitHub zero-day
4. What does the “97 million” figure in the reports represent?
- A) Number of credentials stolen
- B) Dollars lost in the breach
- ✅ C) Monthly download volume of the LiteLLM package
- D) Total number of lines of code leaked
5. What was the behavior of version 1.82.8 that made it particularly dangerous?
- A) It deleted the user’s hard drive
- ✅ B) It installed a
.pthfile that ran the payload on any Python invocation - C) It only ran when the
litellmlibrary was imported - D) It sent spam emails to all of the user’s contacts
6. Which hacking group claimed responsibility for the attack?
- A) Lazarus Group
- ✅ B) TeamPCP
- C) ShinyHunters
- D) LulzSec
7. Where was the stolen data sent?
- A) The official LiteLLM server
- ✅ B) A lookalike/malicious domain (e.g.,
models.litellm.cloud) - C) The GitHub repository
- D) It was stored locally for later retrieval
8. What should a user do if they installed an affected version?
- A) Just delete the
litellmfolder - ✅ B) Uninstall the package, remove persistent artifacts, and rotate all secrets/API keys
- C) Change only their GitHub password
- D) Reinstall Windows immediately
9. What type of data was NOT reported as being targeted by the credential harvester?
- A) SSH keys
- B) Cloud credentials (AWS/GCP)
- ✅ C) Personal photos and videos
- D) Kubernetes configuration files
10. How long were the malicious packages available on PyPI?
- A) One week
- ✅ B) Approximately three hours
- C) 24 hours
- D) Less than 15 minutes
11. Which tool found in the CI/CD pipeline was the “patient zero” for this cascading compromise?
- A) Snyk
- B) CodeQL
- ✅ C) Trivy
- D) Docker Desktop
12. What is the “last known clean” version of LiteLLM recommended for use?
- A) 1.82.8
- B) 1.82.7
- ✅ C) 1.82.6
- D) 1.80.0
13. What triggered the initial discovery of the attack?
- A) A message from the hackers
- ✅ B) A memory exhaustion bug that caused a developer’s machine to crash
- C) A routine security audit by PyPI
- D) A customer support ticket
14. What did the malware attempt to do within Kubernetes clusters?
- A) Mine Bitcoin
- ✅ B) Create a privileged Pod in the
kube-systemnamespace - C) Delete all existing Pods
- D) Encrypt the cluster with ransomware
15. Why were LiteLLM Docker proxy users generally safe?
- A) Docker images are impossible to hack
- ✅ B) They typically use pinned versions in their
requirements.txt - C) The proxy does not use Python
- D) The attacker forgot to target Docker
16. What is “vibe-coding” in the context of recent AI security discussions?
- A) Coding while listening to music
- ✅ B) Using AI agents to generate and execute code on the fly with minimal human oversight
- C) A new encryption algorithm
- D) A social media trend for developers
17. What kind of persistence did the malware seek on local machines?
- A) Hiding in the BIOS
- ✅ B) Creating a systemd user service and a script in
~/.config/sysmon/ - C) Modifying the Chrome browser settings
- D) Renaming the
python.exefile
18. According to cybersecurity experts, what is the best way to prevent future supply chain attacks?
- A) Never use open-source software
- ✅ B) Pin dependencies to specific versions and use hash verification
- C) Only download code from GitHub, never PyPI
- D) Write all libraries from scratch
19. What was the approximate volume of data reportedly stolen by the attackers?
- A) 1TB
- ✅ B) 300GB
- C) 10GB
- D) 500MB
20. True or False: The official LiteLLM GitHub source code was modified by the attackers.
- A) True
- ✅ B) False (The attack bypassed GitHub and went directly to PyPI)
Answer Summary:
The LiteLLM incident highlights the vulnerability of the AI development ecosystem. While the 97 million downloads emphasize the reach, the 500,000 impacted machines show the real-world scale of this supply chain failure.
As You seek understanding and clarity in your life you should always turn to your Heavenly Father for Guidance
Table of Contents
- Youtube Video (Todays Message)
- Are You Your Own Worst Enemy?
- Women are looking for a fathers love
- Spiritual Order – In The Family and Church
- How God Commands Us To Forgive Those Who We Have Resentment Toward
- Join Our Newsletter
- Top Seven Articles
- Our Mission Statement
- Our Vision
- Tithing And Giving!
When Tithing please give what you feel is good to the amount we are helping you in your spiritual life.

Here is a YouTube video to help theses who need to understand someone explaining the important message, the YouTube video is called, “AI Hacked! LiteLLM COMPROMISED! 97 Million Potentially Exposed”, This video is with STARTUP HAKK YouTube Channel:
Note: MadeManMinistries.com has no relations with STARTUP HAKK YouTube Channel, but MadeManMinistries.com enjoys sharing the word.
Note: We do use YouTube Video’s under the “Fair Use” Act under the Copyright Law:
“Fair use is a doctrine in the United States copyright law codified in Section 107 of the Copyright Act of 1976.1 It provides for the legal, non-licensed citation or incorporation of copyrighted material in another author’s work without requiring permission from the rights holders, such as for commentary, criticism, news reporting, research, teaching or scholarship.01 The U.S. Copyright Office Fair Use Index should prove helpful in understanding what courts have to date considered to be fair or not fair but it is not a substitute for legal advice.2“

This is a major important point about forgiveness
Leave there thy gift before the altar, and go thy way; first be reconciled to thy brother, and then come and offer thy gift. -MATTHEW 5:24 KJV
Are You Your Own Worst Enemy?
I would start out by saying what Jesus Christ would want us to do? Pray and how should we pray? The Lord’s Prayer, and how often should we pray? Continually. Why do we use the Lord’s Prayer and not some other? The Lord’s Prayer covers all the areas that is important for our spiritual being.
When we pray the Lords prayer we ask to forgive our enemies, let God’s will be done, the kingdom to come. By praying the Lord’s prayer we let go of many thoughts we have in our head and give them back to God so we can have things revealed to us.
We must overcome resentment in our heart, and in a past video I shared about Dr. Jordan Peterson talks about how resentment can destroy us and we become our own very worst enemy and Jordan goes on to say that we must talk to people what we have resentment toward to overcome that resentment. Other people who lived in the past who talked about this is Jesus Christ and someone who is living now who talks about this daily is Brother Augustine, Dr. John MacArthur, Dr. Charles Stanley, Rev. John Piper and Pastor Paul Washer.
Women are looking for a fathers love
Women are looking for a fathers love. Its important that men understand women are looking for a fathers love and not get screwed. Woman more than anything are looking for a strong spiritual man to lead the future (the family). I think in many YouTube videos on biblical teachings, how young women are being hurt by men that are just looking to get laid instead of doing right and being in Christ and setting a good example of a strong man. We must be in Christ, hate no one, love all, forgave theses we resent, love what is right and support people who are walking with God.
Women need their fathers in their lives to be strong man to be good examples and not BETA men or weak examples of what a man should be. Its important that a man leads the way as Christ leads men, we as man need to fellow Jesus Christ to keep society from going to HELL.
Every day you can see or people watch how some men and women our living in hell without the right spiritual order then you will continue your hellish way according to 2 Peter. You can also find it in Romans. God will give you over to a reprobate mind.
And even as they did not like to retain God in their knowledge, God gave them over to a reprobate mind, to do those things which are not convenient. – Romans 1:28 (KJV)
In Romans 1, Paul refers to something known as a reprobate mind. If you’re not familiar with the term reprobate, the literal definition in the Greek is failing to pass the test, unapproved, counterfeit.
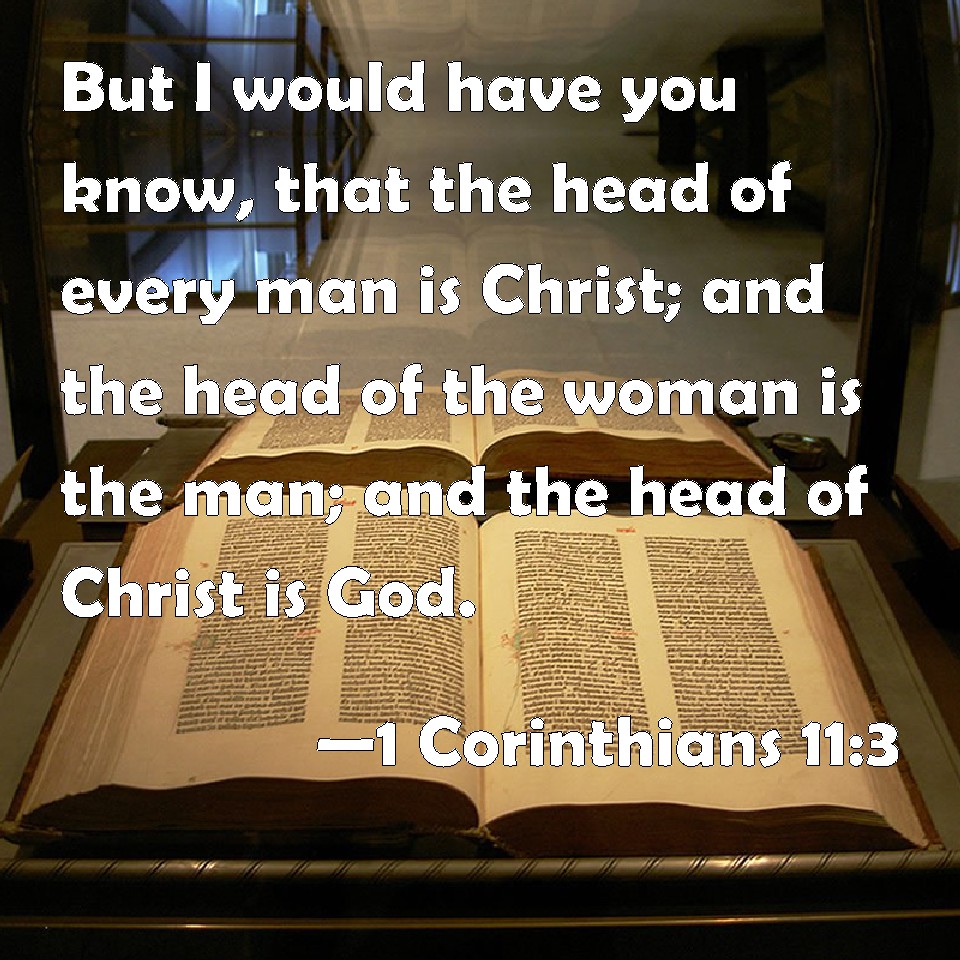
Spiritual Order – In The Family and Church
God the father
Jesus Christ
Father (Men over women)
Mother (Women over children)
Here is Book, Chapter and Verse from the Kings James Version 1 Corinthian 11:2-16, But the main message is in 1 Corinthian 11:3: “3 But I would have you know, that the head of every man is Christ; and the head of the woman is the man; and the head of Christ is God.”
A Woman Conferring The Spiritual Order According to Saint Paul And How The War On The Family Is Being Wage:
How You Treat People Is Who You Are! On Judgement Day You Will Be Judged How You Treated The Less Fortunate (Open Letter)
New Social Contract To Save The West!
Should America And The Western World Have A New Social Contract? (Open Letter)
Father’s Rights
GARBAGE GENERATION

GARBAGE GENERATION By Daniel Amneus
$15.95 Price Check Ebay.com
Daniel Amneus – The Garbage Generation.pdf Link
Back to Patriarchy!

Back to Patriarchy! by Daniel Amneus
$29.95 Price Check Ebay.com


Check out our newest website CIPADS.com place ads for business, jobs, real estate or another site like craigslist
How God Commands Us To Forgive Those Who We Have Resentment Toward.
All of us are tested everyday by our personal internal struggle coming from resentment of what happened earlier in our lives as children typically what our mother did to us, telling how our fathers were not good enough or driving us away from our fathers when we were children. We most go to the people that we have resentment against and forgive them. By forgiving our mothers or whoever we have resentment against, God will forgive us and we can return to the heavenly Father through our Lord and Savior Jesus Christ.
It was said if you don’t love everyone then you love no one. People today live like the Old Testament people did. We must forgive and love everyone as God Commanded us to do according to Matthew 22:34-40.
After Reading The Passage I would Recommend Doing A Silent Prayer
Its is said: Be still, and know that I am God: I will be exalted among the heathen, I will be exalted in the earth. Psalm 46:10 King James Version (KJV)

Jesus is an example of a Fathers loves
Join Our Newsletter
Top Seven Articles
- The Problem With Older Women Liking/Dating Younger Men
- I Dream A Dream That All Men Would Have Love For One Another
- IF by Rudyard Kipling (A Life Changing Poem)
- HOW to be PERFECT… According to Jesus Matthew 5:43-48
- Let Women Come To You
- The Willful Submission of a Christian Wife (Ephesians 5:22-24)
- The Greatest Mistake Man Has Ever Made?
The List Children Of The Lie!!
The List Children Of The Lie!!
People of the Lie : The Hope for Healing Human Evil
Average Rating: (3.6) stars out of 5 stars
$17.93 Buy now price check at Walmart
Special Articles:
Who Was Jezabelle In The Bible?
Is Malachi An Indictment Against Mankind?
What does the Bible say about breaking generational curses?
Its Time To Repeal Women’s Rights To Contact Your Elected Official
Is It Time To Establish Israel/The New Jerusalem As Head Of The World
The Terrifying Truth About The Antichrist
Sexual Revolution, Perverted Revolution, Then Reprobates
Are The Black Hebrew Israelites The Synagogue of Satan Accusation in Revelation 2:9?
A Wife Should Be “A Mirror” To Her Husband?
Ethoipian Bible Was Never Translated In To English
Heretic Series/Beware Of The Wolf In Sheeps Clothing
Is The Mormon Church Heretics? Of Arianism Heresy
Is Rev. Robert W. Lee A Heretic?
Does Gino Jennings Know Hes a Heretic? Of The Arianism Heresy Part Two
Is Islam And All Muslims Heretics? Of Arianism Heresy
Is Gino Jennings A Heretic? Of Arianism Heresy
Is Jesse Lee Peterson A Heretic? Of Arianism Heresy
Who Are the 5 percenter or 5%? Are They Heretics
Who Is Billy Carson? Why Does Billy Teach A Different Gospel Of Our Lord Jesus Christ?
In a world where it is so easy to forget the importance of God, we must remember that He is holy and will not share His glory. America has forgotten this truth and it is time for us to re-examine our relationship with God and recognize that He is the one true God who deserves our full devotion and reverence. We must remember that He will not be taken lightly or ignored, but rather should be honored as the Creator of all things. Only then can we truly experience His love and grace in our lives.
America Has Forgotten! That God The Father Is Holy And He Will Not Share His Glory!
God Reveals Himself
Click the link about a PDF how God reveals himself to you: God Reveals and Satan Speaks to you!
Our Mission Statement
Uniting men of good character who, though of different ethnic or social backgrounds, share a belief in the fatherhood of God and the brotherhood of mankind. Bring Men back to the Father and sharing the biblical view of the Heavenly Father.
Our Vision
By returning to our heavenly father God thru the Lord and Savior Jesus Christ we can rebuilt the family, once the man is recognized as the head of the family and household. Partner with us as we develop a community, mission, and leadership support for the men of today.
Now is the time for a new movement of men. As brothers, fathers let’s become who we’re created to be, knowing our identity, purpose, and destiny in Christ. Then let’s do, linking arms to change the world for good … and for God. Help bring transformation and revival to our families, churches, and communities.

Tithing And Giving!
When Tithing please give what you feel is good to the amount we are helping you in your spiritual life. We are a for profit Ministry meaning we take all profits or donations and give it back to the community we service. Please visit our sponsors down below or along the side of the website, Thanks.

Save Up To 60% Off Hotels, Flights, Cruises, Rental Cars